The Ultimate Guide to Endpoint Detection and Response
2025 edition
Overview
Also known as EDR.
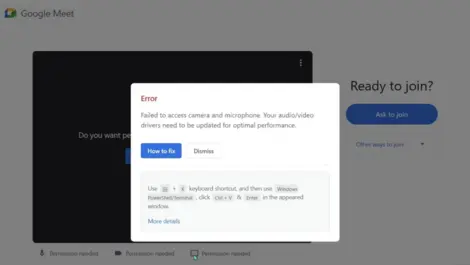
End points are the pointy end of the network and are often quite literally found in the user’s hands – as a laptop, smartphone, or other access device. Endpoints can also include IoT sensors or any other connected item, including printers and other peripherals. Endpoint Detection and Response is the cybersecurity technology responsible for monitoring, detecting, and addressing malware at device level.
Analyst reports

Gartner on EDR & Firewalls
SentinelOne named a Customers' Choice in 2025 Gartner X...
Last week

CONTEXT on EDR & SaaS
SaaS growth offsets IaaS slump in Western European clou...
Last month

Gartner on EDR & Malware
Why is ransomware still a thing in 2025?
Last month

Gartner on EDR & Endpoint Protection
Bitdefender Launches PHASR to Fight Stealthy Cyber Thre...
Fri, 25th Apr 2025

AV-TEST on EDR & DevOps
Kaspersky tops 2024 security tests with record 97% TOP3...
Thu, 17th Apr 2025
Expert columns
By Dakshitaa Babu of SquareX
Why ClickFix attacks are outpacing enterprise security
Fri, 21st Mar 2025

By Edgar Zacharjev of Pulseway
From AI to automation: How Pulseway redefines IT remote...
Fri, 28th Feb 2025

By Steve Moros of Proofpoint
DeepSeek's rise: Navigating the AI data and security ch...
Tue, 11th Feb 2025

By Sadiq Iqbal of Check Point Software Technologies
From deepfakes to ransomware: The key trends which will...
Mon, 9th Dec 2024

By Gareth Cox of Exabeam
Stretching the SOC’s ability to cover more threats
Wed, 4th Dec 2024
More expert columns

By Simon Howe of ExtraHop
Guarding against ransomware in the midgame
Thu, 14th Nov 2024

By Steve Katanas of HID
Enhancing data centre security with mobile access contr...
Mon, 30th Sep 2024

By Steve Moros of Proofpoint
The insider threat: Why Australian businesses are most ...
Wed, 25th Sep 2024
By Innes Muir of Logpoint
How MDR will transform cybersecurity in the mid-market
Mon, 16th Sep 2024

By Devasmita Das of ColorTokens
Beyond prevention: Why breach readiness is your cyberse...
Mon, 19th Aug 2024

By Trevor Dearing of Illumio
Why the answer to AI threats is not more AI
Fri, 28th Jun 2024
Recent news

About Customers
N-able launches free global UEM certification for IT st...
Yesterday

About Bring Your Own Device
Portnox & CrowdStrike team up for real-time access cont...
Yesterday
About Endpoint Protection
Bitdefender unveils upgrades to partner & MSP programme...
Last week
About Misinformation
Safari users at heightened risk from new fullscreen Bit...
Last week
About Malware
Fake AI social media ads spread malware to millions glo...
Last week
More news

About Firewalls
Sophos partners with Capsule to streamline cyber insura...
Last month

About Software-as-a-Service
Acronis reaches 300 technology integrations in expandin...
Last month

About Productivity
Gordon Murray Group streamlines IT operations with Apog...
Last month

About Data Analytics
Tenable One platform adds connectors & custom risk dash...
Last month

About Software Updates
Cloudflare, Microsoft & police disrupt global malware s...
Last month
Even more news

About Ransomware
Ransomware attacks on industrial targets surge, AI tact...
Last month

About Gaming
AMD unveils new Radeon, Ryzen & AI PC innovations at Co...
Last month

About Cloud Services
Acronis partners with Adelaide Crows to boost cyber sec...
Last month

About Endpoint Protection
Kaspersky Endpoint Security achieves full marks in tamp...
Last month

About Security intelligence
Tenable One unifies risk data with new connectors & das...
Last month
Job moves

Move at Saatchi & Saatchi
Whip Around appoints new directors as global expansion ...
Last month

Move at Pure Storage
Ekco appoints cloud industry veteran Ben Savage as CEO ...
Last month
Move at Palo Alto Networks
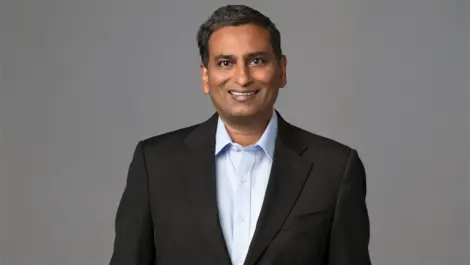
WatchGuard CEO Prakash Panjwani steps down as Vats Sriv...
Last month

Move at RMM
Andre Schindler promoted to SVP at NinjaOne amid growth
Fri, 6th Sep 2024

Move at Bitdefender
WithSecure appoints Samantha Cotton as UK & Ireland cha...
Fri, 16th Aug 2024
Other guides
You can read other related guides from Cybersecurity, Advanced Persistent Threat Protection, Artificial Intelligence, Extended Detection and Response, and Breach Prevention.
Powered by